
Access Control Installation
NYC’s Trusted Access Control Installer — Available Around the Clock.
From fingerprint and facial recognition biometrics to keycard readers, mobile credentials, and cloud-based management, our certified technicians design and install access control systems that give you precise control over who enters every door — at any scale.
Why Choose Lock & Tech USA
Since 1998, we’ve been securing homes and businesses across NYC and New Jersey with professional security solutions you can trust. Our licensed technicians provide 24/7 emergency service, using only the latest technology and backed by comprehensive warranties on all installations.






No Matter Your Access Control Need, You Can Count on Us
- Your business requires biometric fingerprint or facial recognition readers at secure entry points
- You want keycard or key fob access replacing traditional lock-and-key entry
- Your team needs mobile credentials to unlock doors using their smartphones
- You need cloud-based management to add or revoke access instantly from anywhere
- Your facility requires multi-level access with different permissions per zone or floor
- You want a keypad system installed as a standalone or secondary access method
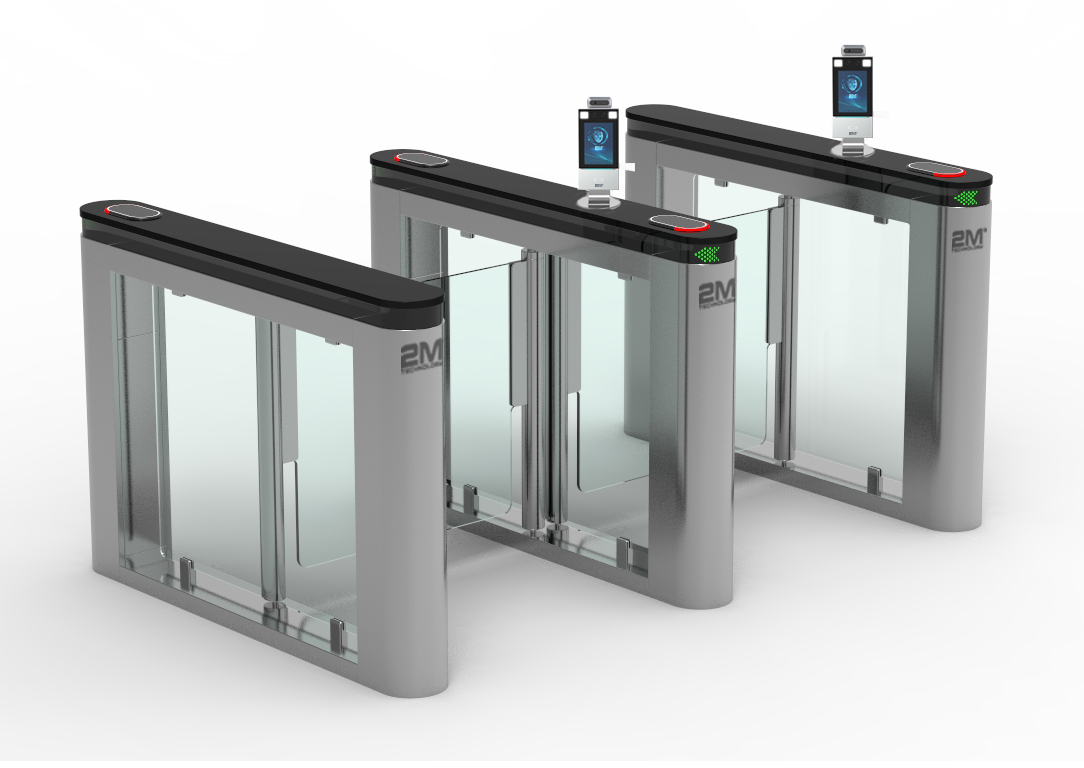
- Your elevator, turnstile, or gate needs electronic access control integration
- You need palm vein or iris scan readers for maximum-security restricted areas
- Your system needs to integrate with cameras that record every access event
- You want detailed access logs showing who entered which door and when
- You need a fully customized system designed around your specific security requirements
Lock and Tech USA – Your Trusted Partner in Access Control Solutions
At Lock and Tech USA, we understand the importance of safeguarding your business, home, or any other secured environment. That’s why we specialize in providing state-of-the-art access control solutions that offer complete peace of mind.
Access Control Systems Tailored to Your Needs
Lock and Tech USA offers a comprehensive suite of access control systems, including biometric scanners, card readers, electronic locks, and more. Our systems are designed to ensure that only authorized individuals can access specific areas, thereby providing an enhanced layer of security.
Whether you need to protect a single office or a sprawling industrial complex, we have the expertise and technology to create a tailored solution that fits your unique requirements.
Why Choose Lock and Tech USA for Access Control?
- Cutting-Edge Technology: Our access control solutions are built using the latest technologies, ensuring reliable performance and seamless integration with existing security infrastructure.
- Expert Installation and Support: Our skilled technicians provide professional installation, maintenance, and 24/7 support to ensure that your access control system is always operating optimally.
- Customized Solutions: We work closely with you to understand your specific needs and design a system that provides the exact level of control and security you require.
- Commitment to Quality: With years of experience in the industry, Lock and Tech USA prides itself on delivering high-quality products and services, all backed by our satisfaction guarantee.
- Compliance and Standards: We adhere to all local, state, and federal regulations, ensuring that our systems meet or exceed industry standards.
Access Control for a More Secure Tomorrow
With Lock and Tech USA, you can be confident that your premises are protected by the most advanced and reliable access control systems available. We work with businesses and homeowners across various industries, delivering solutions that are not just robust and efficient but also easy to use.
Contact us today to discuss your access control needs, and let Lock and Tech USA design a security solution that empowers you to control access to your premises with complete confidence.
Biometric Access Control Systems
What is biometric access? It’s one of the most popular types of security systems on the market. It’s a combination of security and convenience that no other security system can replicate.
Access control is the management of an access point whether that is a door, security turnstiles, elevator, or other access points where only authorized users are allowed in. While access control systems in New York can be set up for just about any access point that uses an electronic locking mechanism, doors are the most common applications for access control.
Types of biometric access include:
- Palm vein – A relatively new form of biometric that uses infrared light to map the unique vein pattern in the palm of your hand. Unlike other biometrics, this one is inside your body which gives it a lot of advantages and makes it great for access control systems.
- Fingerprint – The most common and what most people think of when they think of biometrics. It’s an old, time-tested biometric. Even the Ancient Chinese used fingerprints to authenticate government documents and the Babylonians used them to sign contracts.
- Iris scan – A highly patterned and unique use of biometrics. Iris scanners use infrared lights and high-resolution cameras to make a highly detailed map of the iris, which is then converted into information to create a person’s biometric ID.
- Face recognition – Face recognition has become very popular lately. In airports, airlines are using facial recognition to identify travelers, reducing lines to allow them to travel more quickly. There’s controversy with this form of biometric because of privacy concerns. Facial recognition can be captured at a distance which makes it possible to capture someone without their consent.
Why Are Biometrics Used in Security Systems?
Traditional access systems are subject to a very strong point of vulnerability: objects and data can be shared or stolen, giving access to an unwanted person. Depending on the level of security, this might not be the biggest deal, but it’s still cause of concern.
Sure, if you’re running a coffee shop and have an added level of security on the bathroom door, then biometrics might be overkill. But if you need to provide access to a limited number of people for something more important, then a keypad isn’t going to hold up to the scrutiny of the security needed. That’s the problem with passcodes. They can be shared with anyone very easily.
Physical access tokens like keycards, fobs, or ID cards are a step in the right direction but are also vulnerable. They can easily be lost or stolen and provide access to whoever holds the key, whether they’re the person who’s authorized to use the key or not.
Biometrics don’t have these vulnerabilities though. Your unique biometric code is always with you. You can’t write down your iris on a sheet of paper and give it to someone else or lose your fingerprints for someone else to steal.
While all biometric systems aren’t created equally, even the least secure biometric system is still more secure than traditional forms of security.
What are the Benefits of Using Biometrics for Access Control?
There are a number of benefits of using biometrics for access control. These include:
Security – Since biometrics use a person’s unique biology for access, it’s extremely difficult to have someone else gain access if their biology isn’t in the system.
- Difficult to duplicate – Traditional access tokens like keycards can be duplicated easily with duplication devices. This means that a lot of more traditional access systems have vulnerabilities. Biometrics are much harder to duplicate, especially since more modern biometrics use liveness tests to ensure that the biometric data is coming from a living human rather than a forgery.
- Easy permission management – With a biometric control system, it becomes easy to deny access directly from the console dashboard, which makes sure that only active, non-suspended users are given access.
- Convenience – Biometric control systems are incredibly convenient with how they allow authorized users to access a control point without needing anything besides themselves. Unlike a keycard, your biometric is always with you.
- Efficiency – Biometrics can identify users in less than a second, eliminating the delays and time inefficiencies caused by manual identity checks, passwords, or PINs.
- Reduced costs – The ease of biometrics means that there’s a lot of costs across the board that can be reduced. A biometric access system means you need less security staff, reduce replacement costs down to zero without a need for keycards, and a biometric system makes for the perfect way to protect expensive property.
Keys, Fobs, and ID Cards
Keycards go by a lot of different names. There are prox cards, swipe cards, and the key fob system. There are also magnetic cards, RFID/NFC cards, and even simple ID cards. Even though they all have different names and they may operate in different ways, they all serve one function: to securely and efficiently grant or restrict access to a certain area.
One of the biggest manufacturers of a card access system is HID Global. They manufacture, distribute and sell access cards to operate a proximity reader. The HID access control system does have a downside: it can be easily hacked by a $10 device. This is because most cards run on the Wiegand protocol, a vulnerable protocol that allows hackers to copy cards and keycards quickly and inexpensively.
What is a keycard? How does it work with a reader?
A keycard is a security token that grants you access through electrically-powered doors. These systems require a keycard reader (installed on the door) and you gain access by either tapping your card on the reader (proximity reader), swiping it (swipe reader), or inserting it (insert reader).
With keycards, users no longer need to insert a metal or traditional key into a tumbler lock to gain access. Instead, there is an embedded access credential on the keycard magstripe, or as a chip in the card itself, and this is read by the keycard reader each time you attempt an unlock. If the unique code on your card is recognized by the reader, permission is granted for access.
How does the Reader communicate with the door lock?
Once the reader recognizes the access credential, it then communicates with the door lock. The smart access control reader will be wired to an electric lock on your door and it will send a signal to the lock to start an unlock event. With a good system, the whole process takes less than a second.
Alternatives to Keycard Entry Systems
Given the disadvantages of keycard entry systems, it’s imperative to identify better alternatives that can address these disadvantages. An attractive option would be mobile access control. This means using the credentials on your mobile phone to unlock doors.
We offer a cloud-based mobile access control systems in New York. This means that, in addition to keycards, users can unlock doors with their cellphones. By using the RFID and Bluetooth chips inside the phone, you can use your phone as you would an access card and tap it to the reader to unlock it.
Moreover, as a cloud-based solution, the management or admins will be able to reap the benefits of having a cloud-based system (as opposed to a traditional local-hosted system). Our access control systems host all the data and offer interesting data analytics and observations.
Get a quote from us and experience the ease and security of a cloud-based mobile access control system.
Keypad Door Control Systems
Pin Pads or keypads for doors are usually connected to either a central access control system in New York, standalone pin pads, keypads on door locks or deadbolts, or IP-connected pin pads. Sometimes they are combined with biometric access systems since PINs can be passed on from one person to the next.
You might be most familiar with keypads on locks in a scenario where you may be at a place of business where you can’t use the restroom unless you buy a drink. In return for buying said drink, they print the code to the bathroom on your receipt. If you’re in there all the time, you might memorize the code since the place most likely rarely changes its codes. That’s the problem with PIN codes. If you change the PIN, no one gets in anymore.
The keypad is a mainstay of access control today as opposed to a push to exit button. The modern office with electronic locks most likely uses a keypad either as a secondary access control option, alongside another form of access control, or as a stand-alone access point. The keypad is integrated into another security system, such as badge readers or a biometric scan of some sort. The ease with which it can be installed makes it very common among electronic locks.
While keypads remain very useful, the reason why they fell in popularity is that it’s not a great security solution. While a keypad does away with physical keys or some other security token, a PIN can be shared with an infinite amount of people, regardless of security level. The entire system hinges on trusting its users with confidential information.
It’s difficult to hold anyone accountable for a breach in security, especially if the PIN is widely spread amongst the user base. Because of these, security tokens have become more prominent for their stronger security features. In addition, there’s been a minimization of inconvenience associated with such tokens, allowing access through your mobile phone or creating a reader that is more sensitive which eliminates the need for scanning keycards in close proximity.
- Free ConsultationSchedule a complimentary on-site assessment to discuss your security needs and concerns
- Custom DesignReceive a tailored security solution designed specifically for your property and budget
- Professional InstallationExpert technicians install your system with minimal disruption to your daily routine
- Testing & TrainingComprehensive system testing and hands-on training to ensure you're fully confident












Mon–Fri: 8 AM – 6 PM
Sat-Sun: Closed
1112 Quentin Rd, Brooklyn, NY 11229
1619 McDonald Ave, Brooklyn, NY 11230
245 E 115th St, New York, NY 10029
117 NJ-35 #11, Keyport, NJ 07735
